
Fingerprint recognition has become one of the most trusted and widely deployed biometric technologies in the world. From access control systems and financial services to mobile devices and government identity programs, it offers a balance of security, convenience, and scalability that few technologies can match.
But behind this seemingly simple “touch-and-go” experience lies a sophisticated combination of image processing, pattern recognition, and algorithmic intelligence.
Understanding the Two Core Recognition Methods
At a technical level, fingerprint recognition systems generally rely on two different approaches to determine identity.
The first is image-based statistical matching. This method treats the fingerprint as a whole image and compares it directly with another fingerprint image. By analyzing the overall similarity between the two, the system determines whether they belong to the same person. While relatively straightforward, this method is more sensitive to noise, distortion, and environmental conditions.
The second, and more widely used approach today, is feature-based matching. Instead of comparing entire images, the system extracts unique structural details from the fingerprint and compares those features. These include:
* Global features, such as the overall pattern (loops, whorls, arches)
* Local features, also known as minutiae points, such as ridge endings and bifurcations
This approach is significantly more robust and accurate, making it the foundation of modern fingerprint recognition systems.
The Complete Fingerprint Recognition Process
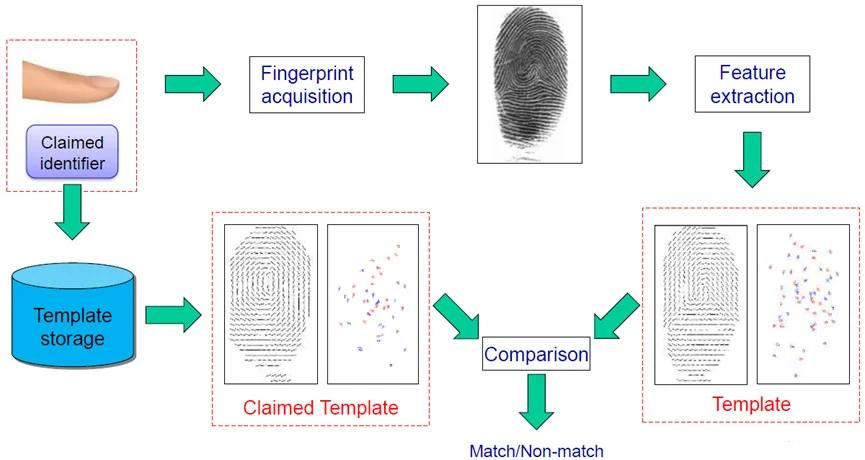
A fingerprint recognition system follows a structured workflow to transform a raw image into a reliable identity decision.
It begins with image acquisition, where a fingerprint sensor captures the user’s fingerprint. The quality of this step directly impacts the overall system performance.
Next comes image preprocessing. Fingerprint images often contain noise caused by skin condition, pressure, or environmental factors. Advanced preprocessing techniques enhance ridge clarity and remove noise, producing a clean and usable image.
The system then performs feature extraction, identifying and digitizing the unique points within the fingerprint. These data points form a compact and secure template that represents the fingerprint.
Finally, during feature matching, the extracted template is compared against stored templates in a database. Based on the similarity score, the system confirms or rejects the user’s identity.
Hardware Architecture: Single-Chip vs. Multi-Chip Solutions
The evolution of fingerprint recognition technology has led to two main hardware architectures: single-chip and multi-chip solutions.
Multi-chip systems separate sensing, processing, and control functions across different components. While flexible, they tend to be more complex and costly.
In contrast, single-chip solutions integrate all key functions into one compact unit. This integration reduces manufacturing cost, improves processing speed, and simplifies system design. As semiconductor technology continues to advance, single-chip solutions are rapidly becoming the industry standard—especially for cost-sensitive, large-scale deployments.
Why Sensor Size Matters in Cost Optimization
Another critical factor in fingerprint module design is the sensor area.
In semiconductor manufacturing, a larger sensor occupies more space on a wafer, which means fewer chips can be produced from a single wafer—leading to higher costs. Conversely, smaller sensors allow more units to be produced, significantly improving cost efficiency.
Traditionally, reducing sensor size could compromise performance. However, with modern algorithm advancements, even small-area sensors can deliver high accuracy, making them ideal for scalable commercial applications.
The Role of Algorithms in Performance and Accuracy
Ultimately, the true intelligence of a fingerprint system lies in its algorithm.
A well-designed algorithm ensures that the system maintains a low False Rejection Rate (FRR)—so legitimate users are not denied access—and a low False Acceptance Rate (FAR)—so unauthorized users cannot gain entry.
In the industry, companies typically adopt one of two strategies:
- Developing proprietary algorithms, allowing full customization and optimization
- Licensing proven third-party solutions, such as those from Precise Biometrics
Third-party algorithms can deliver excellent performance, particularly with active sensors. However, they often come with licensing costs and may not be fully optimized for all hardware types, especially passive or purely capacitive sensors.
A Balanced Approach to Modern Biometric Systems
Fingerprint recognition technology today is no longer just about capturing an image—it is about achieving the right balance between hardware design, sensor optimization, and algorithm performance.
With the continued advancement of single-chip integration, compact sensors, and intelligent algorithms, modern fingerprint solutions are becoming more affordable, scalable, and reliable than ever before.
For businesses looking to deploy biometric systems—whether in security, fintech, or smart infrastructure—fingerprint recognition remains a proven, future-ready choice.